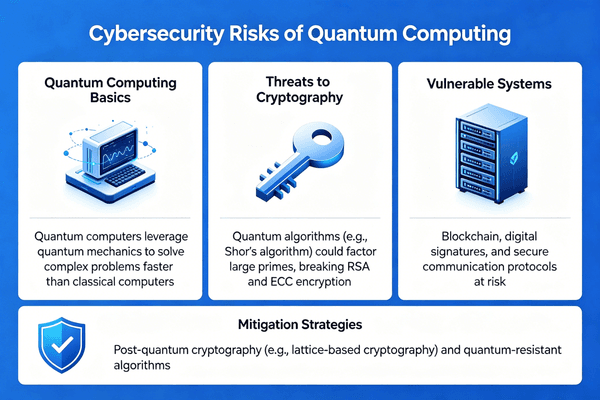
You trust your data is safe. But quantum computers1 can break today's locks. We must upgrade our hardware now before hackers steal everything.
Quantum computing threatens cybersecurity because quantum algorithms can easily break standard RSA encryption. This puts global data at risk. To fix this, the tech industry is rapidly developing Post-Quantum Cryptography (PQC)2 chips to protect hardware and secure our future digital supply chain.
You might think this is a problem for the distant future. But the countdown has already started. If we do not act today, every piece of data we protect will become an open book. Let us explore why this happens and how we can stop it.
Why is Current RSA Encryption Failing Against Quantum Algorithms?
Hackers record your encrypted data today. They wait for quantum machines to decode it tomorrow. We need new defenses because our current math is too weak.
RSA encryption relies on factoring large prime numbers, which takes regular computers thousands of years. However, a quantum computer uses Shor's algorithm3 to solve this in hours. This means standard security protocols will fail completely when powerful quantum machines arrive.
The Math Behind the Quantum Threat
I have spent over 20 years in the electronic components industry. I see how much we rely on standard security chips every single day. Today, OEMs and hardware engineers use standard microcontrollers with RSA encryption. This system works well against normal computers. Normal computers try one key at a time. They are slow.
But quantum computers1 work in a completely different way. They use qubits. Qubits can look at many keys at the exact same time. This makes them incredibly fast at solving complex math problems. When I talk to our clients at Nexcir, I always warn them about the "Harvest Now, Decrypt Later4" attack. Bad actors steal encrypted data now. They store it. They wait for quantum computers1 to become cheap and available. Then, they unlock your data.
This is a massive risk for automotive and IoT devices. These devices have very long life cycles. If you build a smart car today, it will still be on the road in ten years.
Comparing Regular and Quantum Threats
Here is a simple look at how these two threats compare in our industry:
| Feature | Regular Computer Threat | Quantum Computer Threat |
|---|---|---|
| Speed to break RSA | Millions of years | A few hours or days |
| Method used | Trial and error guessing | Shor's advanced algorithm |
| Risk level today | Low | High (Future threat) |
We must think ahead right now. We need to plan our hardware choices carefully. We want to avoid these future risks before they happen.
What Are the Real-World Dangers of Quantum Cyber Attacks?
Imagine losing control of your smart factory or connected car. Quantum hackers can bypass old security chips. You must know the risks to protect your production lines.
A quantum cyber attack5 can compromise financial records, medical data, and industrial control systems6. Hackers can forge digital signatures7 and send fake software updates to IoT devices. This puts OEM hardware8, connected cars9, and global supply chains at severe risk of total shutdown or control loss.

How Hackers Target Hardware
In my daily work, I help production teams source reliable PMICs, sensors, and microcontrollers. These teams always worry about supply risks and part shortages. But security is also a huge supply chain risk10 that many people ignore. If a hacker breaks the digital signature of a hardware device, they can pretend to be the original manufacturer.
They can send fake firmware updates11 to connected cars9. They can send bad code to smart factory machines. The device will accept the update because the signature looks real. This is very dangerous for everyone. It can stop an entire factory from working. It can make a car crash on the highway.
The Impact on Different Industries
We need to look closely at which sectors face the most danger. I break it down like this for our OEM clients:
| Industry | Main Cyber Risk | Impact Level |
|---|---|---|
| Automotive | Fake over-the-air (OTA) updates | Critical |
| IoT Devices12 | Total loss of device control | High |
| Industrial | Factory and machine shutdowns | Critical |
| Consumer Tech | Stolen personal user data | Medium to High |
We must protect these industries with better hardware. Hardware engineers cannot just trust old security methods anymore. We need to find new, secure components. These components must last for many years in the field.
How Do Post-Quantum Cryptography Chips Solve This Problem?
Your old security chips will soon be useless. This puts your whole product at risk. PQC chips13 use new math that even quantum computers1 cannot break.
Post-Quantum Cryptography (PQC)2 chips are hardware components designed to run advanced mathematical algorithms. These new algorithms are resistant to quantum attacks. By upgrading to PQC chips13, engineers can secure their devices, protect digital signatures7, and ensure long-term safety against future quantum hackers.
The Shift to PQC Hardware
This is where the real solution begins for our industry. To stop quantum attacks, we must change the physical hardware. Software updates are simply not enough. The industry is now forcing the rapid research and development of PQC chips13. PQC stands for Post-Quantum Cryptography.
I always advise my clients to look for hardware that supports these new PQC standards. PQC uses different types of math. It uses lattice-based cryptography14. Quantum computers are very bad at solving these specific math problems. They cannot break the new locks.
When we source components at Nexcir, we always look for original semiconductors that offer long lifecycle availability. Now, we also actively look for chips that include PQC features. This helps our clients build safe products for the future.
Old Chips vs. PQC Chips
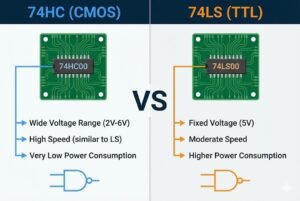
Here is why you need to transition your designs to PQC chips13:
| Feature | Standard RSA Security Chip | New PQC Ready Chip |
|---|---|---|
| Math Basis | Factoring large prime numbers | Complex lattice-based math |
| Quantum Safe | No | Yes |
| Best Use Case | Short-term consumer products | Long-life products (Cars, IoT) |
| Future Risk | Very High | Very Low |
By choosing PQC chips13 today, you save a lot of money later. You do not have to recall products to fix broken security flaws. You ensure your production schedule stays stable and secure.
How Can You Prepare Your Supply Chain for PQC Chips?
Finding new PQC chips13 is hard. Fake parts and long wait times can ruin your plans. You need a safe supply chain to get real, secure hardware.
You can prepare by partnering with a trusted global distributor15. Look for authentic components and stable pricing. A reliable partner will help you find the right PQC chips13, avoid counterfeit parts, and ensure your production line never stops running during this technology shift.
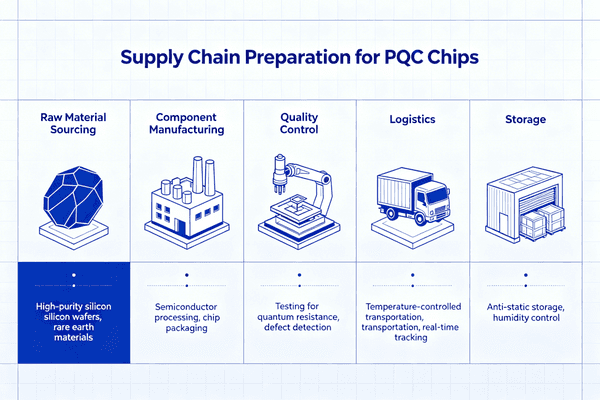
Securing the Right Components
I know that changing your bill of materials is very stressful. Procurement managers face many daily pain points. You want high-quality parts. You want stable prices. You worry about counterfeit products entering your factory. When a brand new technology like PQC comes out, these risks get much worse.
At Nexcir, we solve these exact problems for you. We only use authorized distributors and original component manufacturers. This means every PQC chip we supply is one hundred percent authentic. I always tell my team to check the full traceability of the parts. We want our customers to feel completely safe.
Steps to Upgrade Your Supply Chain
Here is a simple plan I share with hardware engineers. It helps them upgrade their supply chain smoothly:
| Step | Action to Take | Business Benefit |
|---|---|---|
| 1 | Review current MCU choices | Identify weak security risks early |
| 2 | Find PQC chip alternatives | Prepare for future quantum threats |
| 3 | Lock in stable component prices16 | Avoid sudden market price jumps |
| 4 | Use trusted global logistics | Ensure safe and on-time delivery |
We have over 20 years of experience doing this work. We help you find direct alternatives for old parts. We make sure you get the best global logistics support. This way, you reduce your procurement risks. You also stay far ahead of your competitors in the market.
Conclusion
Quantum computers will break old RSA encryption. We must switch to PQC chips13 now. By securing your supply chain today, you protect your products and your future business.
Understanding quantum computers is crucial as they pose a significant threat to current encryption methods, impacting global data security. ↩
Learn about PQC, the future of encryption, which is designed to withstand quantum attacks and secure digital communications. ↩
Discover how Shor's algorithm enables quantum computers to break RSA encryption, posing a threat to current cybersecurity measures. ↩
Explore this strategy where hackers store encrypted data now to decrypt it later with quantum computers, highlighting future risks. ↩
Quantum cyber attacks can compromise critical systems and data. Understanding these dangers is essential for effective cybersecurity planning. ↩
Industrial control systems are at risk from quantum attacks, which can lead to shutdowns and operational disruptions. Learn how to protect them. ↩
Quantum attacks can forge digital signatures, leading to unauthorized updates and security breaches. Learn how to protect against this threat. ↩
OEM hardware is at risk from quantum attacks. Understanding this impact is vital for securing devices and maintaining industry standards. ↩
Connected cars face significant risks from quantum attacks, which can lead to control loss and safety issues. Learn how to mitigate these risks. ↩
Quantum computing introduces new supply chain risks, including counterfeit parts and security vulnerabilities. Learn how to manage these risks. ↩
Fake firmware updates can compromise IoT devices, leading to control loss and security breaches. Learn how to prevent these attacks. ↩
IoT devices are vulnerable to quantum attacks, risking total control loss. Learn how to secure these devices against future threats. ↩
PQC chips are designed to resist quantum attacks, offering enhanced security for long-term device protection. Discover their benefits. ↩
Lattice-based cryptography is a key component of PQC, offering security against quantum attacks. Learn why it's considered quantum-safe. ↩
A trusted distributor ensures authentic PQC chips and stable pricing, crucial for maintaining a secure and reliable supply chain. ↩
Stable component prices help avoid market fluctuations, ensuring a reliable supply chain during the transition to PQC technology. ↩